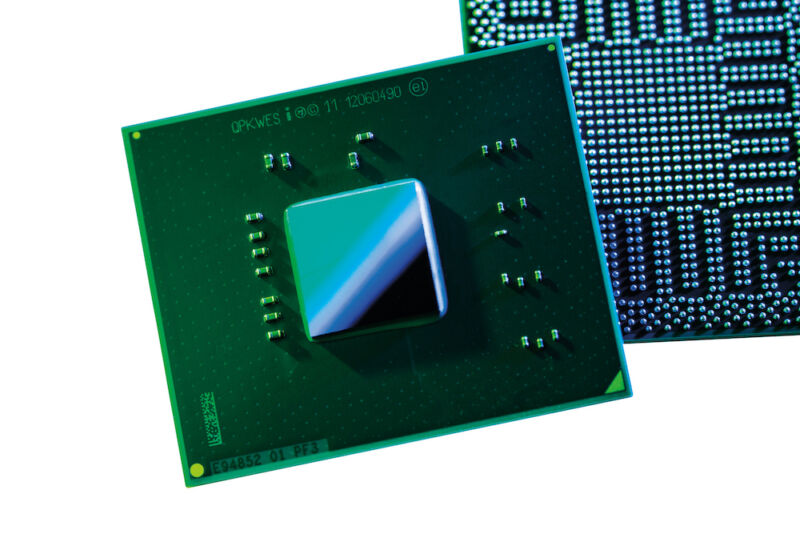
In a first, researchers extract secret key used to encrypt Intel CPU code
Hackers can now reverse engineer updates or write their own custom firmware. …
 reader comments
reader comments
68 with 50 posters participating
Researchers have extracted the secret key that encrypts updates to an assortment of Intel CPUs, a feat that could have wide-ranging consequences for the way the chips are used and, possibly, the way they’re secured.
The key makes it possible to decrypt the microcode updates Intel provides to fix security vulnerabilities and other types of bugs. Having a decrypted copy of an update may allow hackers to reverse engineer it and learn precisely how to exploit the hole it’s patching. The key may also allow parties other than Intel—say a malicious hacker or a hobbyist—to update chips with their own microcode, although that customized version wouldn’t survive a reboot.
“At the moment, it is quite difficult to assess the security impact,” independent researcher Maxim Goryachy said in a direct message. “But in any case, this is the first time in the history of Intel processors when you can execute your microcode inside and analyze the updates.” Goryachy and two other researchers—Dmitry Sklyarov and Mark Ermolov, both with security firm Positive Technologies—worked jointly on the project.
The key can be extracted for any chip—be it a Celeron, Pentium, or Atom—that’s based on Intel’s Goldmont architecture.
Tumbling down the rabbit hole
The genesis for the discovery came three years ago when Goryachy and Ermolov found a critical vulnerability, indexed as Intel SA-00086, that allowed them to execute code of their choice inside the independent core of chips that included a subsystem known as the Intel Management Engine. Intel fixed the bug and released a patch, but because chips can always be rolled
Continue reading – Article source




