Four months after its debut, sneaky Mac malware went undetected by AV providers
Four months after a mysterious group was outed for a digital espionage operation that used novel techniques to target Mac users, its macOS malware samples continued to go undetected by most antivirus providers, a security researcher reported on Thursday.
Windshift is what researchers refer to as an APT—short for “advanced persistent threat”—that surveils individuals in the Middle East. The group operated in the shadows for two years until August, when Taha Karim, a researcher at security firm DarkMatter, profiled it at the Hack in the Box conference in Singapore. Slides, a brief description, and a report from Forbes are here, here and here, respectively.
A few things make Windshift stand out among APTs, Karim reported in August. One is how rarely the group infects its targets with malware. Instead, it relies on links inside phishing emails and SMS text messages to track the locations, online habits, and other traits of the targets. Another unusual characteristic: in the extremely rare cases Windshift uses Mac malware to steal documents or take screenshots of targets’ desktops, it relies on a novel technique to bypass macOS security defenses. (The above-linked Forbes article has more on how this technique, known as a custom URL scheme, allows attacker-controlled sites to automatically install their malware on targeted Macs.)
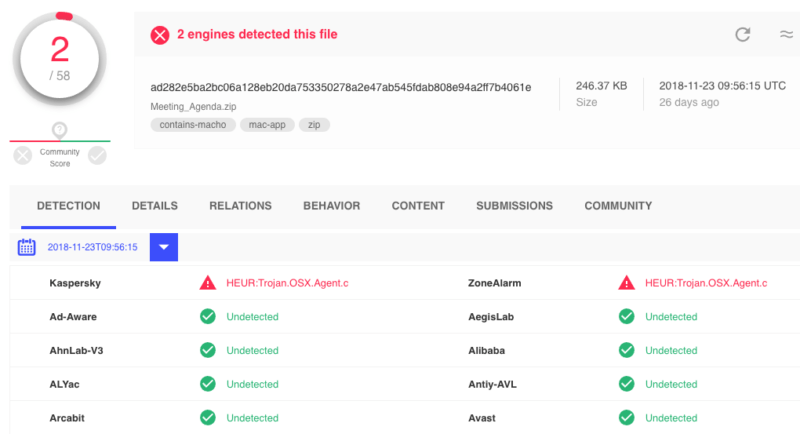
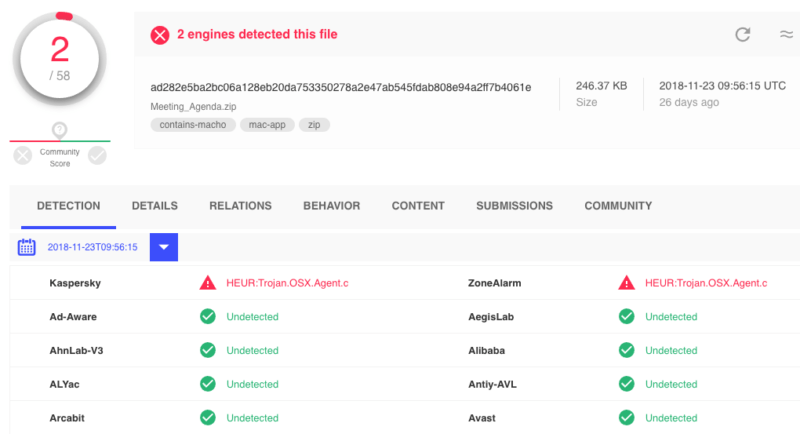
On Thursday, Mac security expert Patrick Wardle published an analysis of Meeting_Agenda.zip, a file Karim had said installed the rare Mac malware. To Wardle’s surprise, results from VirusTotal at the time showed that only two antivirus providers—Kaspersky and ZoneAlarm—detected the file as malicious. Wardle then used a feature that searched VirusTotal for related malicious files and found four more. Three of them weren’t detected by any AV providers, while one was detected by only two providers.
The reason the findings were so surprising is that Apple had already revoked the cryptographic certificate the developers used to digitally sign their malware. That meant Apple knew of the malware. Wardle wrote:
The fact that the signing certificate(s) of all the samples are revoked (CSSMERR_TP_CERT_REVOKED) means that Apple knows about this certificate… and thus surely this malware as well… yet the majority of the samples (3, of 4) are detected by zero anti-virus engines on VirusTotal.
Does this mean Apple isn’t sharing valuable malware/threat-intel with AV-community, preventing the creation of widespread AV signatures that can protect end-users?! 🤔
Narrator: yes
In fairness, the control servers the malware contacts are no longer available on the Internet. That means any infected computers aren’t in danger of being surveilled. Also in fairness, the number of detections has slowly risen in the day since Wardle published his analysis.
Still, the lack of timely detection is troubling, because it suggests Apple isn’t giving AV providers definitions of known malware. Such sharing is a standard practice in the industry and is particularly important in tracking APTs, which by definition are good at concealing their wares from defenders. That failure could prevent targets from knowing they have been infected and taking appropriate steps to protect themselves. Ars asked Apple to comment for this post and received no response. Ars also asked three AV providers if Apple shares definitions, and so far we have not heard back.
“I think [the lack of detections] highlights that traditional AV struggles with new/APT malware on macOS… but also Apple’s hubris,” Wardle told Ars. “We’ve seen them do this before 🙁 It’s disheartening, and somebody needs to call them out on it.”




