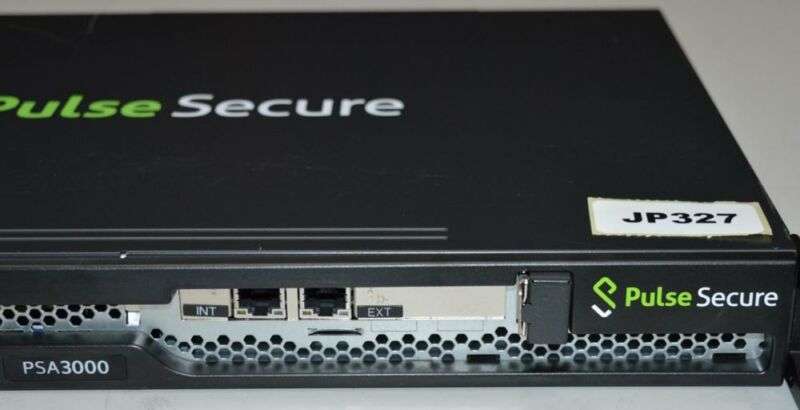
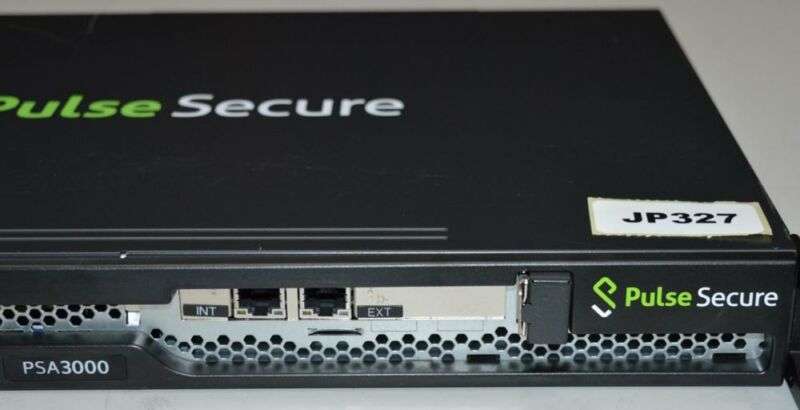
Code-execution bug in Pulse Secure VPN threatens patch laggards everywhere
If you haven’t updated Pulse Secure VPN, now would be an excellent time to do so. …
 reader comments
reader comments
17 with 16 posters participating
Organizations that have yet to install the latest version of the Pulse Secure VPN have a good reason to stop dithering—a code-execution vulnerability that allows attackers to take control of networks that use the product.
Tracked as CVE-2020-8218, the vulnerability requires an attacker to have administrative rights on the machine running the VPN. Researchers from GoSecure, the firm that discovered the flaw, found an easy way to clear that hurdle: trick an administrator into clicking on a malicious link embedded in an email or other type of message.
Phishing season has now officially started
“While it does require to be authenticated,” GoSecure researcher Jean-Frédéric Gauron wrote in a post, referring to the exploit, “the fact that it can be triggered by a simple phishing attack on the right victim should be evidence enough that this vulnerability is not to be ignored.”
Although phishing attacks are old, they’re among the most effective ways to breach the defenses of not just consumers, but Fortune 500 and government organizations as well. The stakes are even higher given the current work-from-home regimen caused by the COVID-19 pandemic.
Last month, attackers took control of Twitter’s internal systems by using detailed personal information taken from social media sites to trick a remote worker into entering credentials into a fake page. According to KrebsOnSecurity, the FBI and the Cybersecurity and Infrastructure Security Agency recently warned that similar attacks were playing out all over the country.
Short for virtual private networks, VPNs allow companies to cryptographically authenticate employees connecting to the network and to encrypt all communications. Over
Continue reading – Article source




